Stop Treating AI Governance as a PDF Problem

Why this matters this week
AI adoption is starting to hit the controls layer of real companies—policy, compliance, security, audit. The tension is becoming obvious:
- Security teams want data retention limits; product teams want bigger context windows.
- Legal wants “no PII ever”; support wants “paste the customer’s full ticket history.”
- Risk wants documented model behavior; engineers are shipping prompt chains that mutate weekly.
This week matters because three trends are converging in live production systems:
-
Vendors are quietly changing their data usage defaults.
“We don’t train on your data” doesn’t mean “we don’t log your data” or “we delete immediately.” Many teams are discovering this mid-audit. -
SOC2/ISO auditors are now asking AI-specific questions.
If you’re in or near an audit cycle, you’re seeing requests like:- “Show me retention configs for your LLM logs.”
- “Show how you prevent customer data from leaving the region.”
- “Show evidence of approval for this model and its use-cases.”
-
Policy PDFs are colliding with prompt templates.
Most orgs now have AI policies written in prose that are impossible to enforce or test. Meanwhile, engineers are wiring SDKs directly to production data.
If you own a production system using LLMs and don’t have privacy & governance wired as code, you’re accumulating opaque risk and probably failing your future self in the next incident or audit.
What’s actually changed (not the press release)
What’s changed in the last 6–12 months isn’t theory; it’s operational reality:
1. Data gravity has shifted to logs and prompts
For “normal” systems, the main risk is in primary databases and backups. For AI systems:
- The riskiest data is now often in:
- Prompt logs
- Intermediate tool call payloads
- Vector store chunks
- Traces captured by observability tools
- These are:
- Spread across multiple vendors
- Poorly classified
- Retained for “debugging” indefinitely
2. “Model risk” has become a control domain
Risk functions are no longer just asking “Do you use AI?” They are tracking:
- Which models (by version) are used where
- Which data can reach which model
- Which outputs are used for which decisions
This is effectively model lifecycle management, and in most orgs it’s currently:
– A spreadsheet
– Some wiki pages
– Tribal knowledge in the head of “the AI person”
3. Privacy expectations got more concrete
Regulators and enterprise customers are asking:
- Where is the model hosted (region, sub-processors)?
- Is training data segregated per-tenant?
- What’s the maximum retention of:
- Raw prompts
- Tool inputs/outputs
- System logs that may contain PII
“Zero data retention” and “no training” flags exist in some platforms now—but they’re not consistently enabled, and they don’t cover all the surfaces (e.g., fine-tuning jobs, eval datasets, embeddings).
4. SOC2/ISO are catching up just enough to be painful
These frameworks are not AI-specific, but auditors are now mapping existing controls to AI:
- Access control: Who can send data to which model provider?
- Change management: Who approved that new prompt chain that now touches HR data?
- Logging & monitoring: Can you reconstruct who saw what and when?
- Vendor risk: How are AI infra vendors reviewed and monitored?
Nothing magical. Just more scrutiny on the weakest, newest parts of your system.
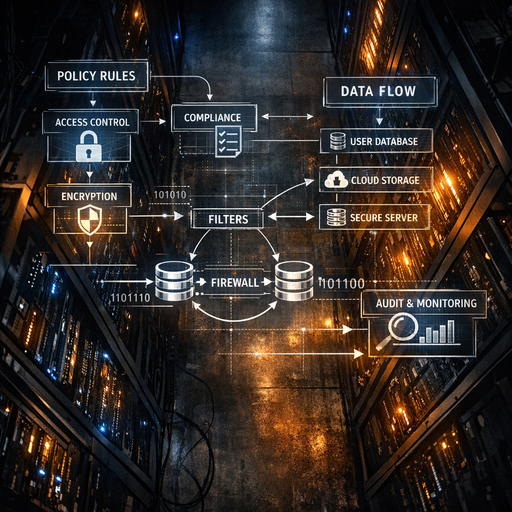
How it works (simple mental model)
Use a three-layer model to think about AI privacy & governance:
1. Data layer: “What can go where?”
Questions:
- What categories of data do you have (PII, PHI, PCI, secrets, internal-only, public)?
- For each category, is it allowed to:
- Leave your VPC?
- Go to a third-party AI provider?
- Be stored in a long-lived index (vector DB, cache)?
- Be used for training/fine-tuning?
Mechanism:
- Policy-as-code for data classification and routing, e.g.:
- “If
data_type == PIIandregion != allowed_region→ reject or redact” - “If
use_case == experimentation→ only synthetic data allowed”
- “If
- Enforced via:
- API gateways
- Middleware in your AI client library
- Connectors to data sources (CRM, ticketing, etc.)
2. Model layer: “Who can use what, for which purpose?”
Questions:
- Which models are approved for:
- Customer-facing content?
- Internal-only assistance?
- Decisions with financial or legal impact?
- What are the constraints:
- Max temperature
- Tool access
- Context sources
Mechanism:
- Model registry + policy:
- Each model entry has:
- Approved use-cases
- Data categories allowed
- Retention expectations
- Vendor risk tier
- Each model entry has:
- Enforcement:
- Don’t let teams call models directly.
- Force all calls through a typed abstraction where the “model choice” is determined by:
- Use-case
- Data sensitivity
- Region/tenant
3. Governance layer: “Can we prove what happened?”
Questions:
- Can you answer, for a single request:
- Which data fields were exposed?
- Which model and version were used?
- Which tools were called and with what parameters?
- Can you:
- Replay a past incident?
- Show auditors that your policies were enforced at time of call?
Mechanism:
- Immutable audit logs covering:
- Input metadata (with sensitive content redacted or hashed)
- Model identity + version
- Policy decisions (allow/deny/transform + rule IDs)
- Tool calls (names, not secrets)
- Stored with:
- Retention aligned with your compliance needs
- Separation between:
- Debug traces (short-lived)
- Compliance logs (longer-lived, more minimal)
If you wire these three layers, “governance” stops being a document and becomes a set of enforceable interfaces.
Where teams get burned (failure modes + anti-patterns)
Some recurring patterns from real deployments:
1. “We’ll just log everything for now”
Pattern:
- Engineering logs full prompts, database rows, and tool responses to:
- Observe model behavior
- Debug prompt chains
- No scrubbing, no truncation, no differential retention.
Failure mode:
- Six months later:
- A support ticket uncovers that raw medical or HR data is in log indexes.
- Legal realizes those logs are replicated cross-region and backed up indefinitely.
- Deletion requests (“right to be forgotten”) can’t be honored.
Anti-pattern smell: “We need all the data to improve the system.”
Better: Minimal logs + structured, redacted traces with adjustable retention windows.
2. “Policy in wiki, code in SDK”
Pattern:
- Company publishes an “AI Acceptable Use Policy.”
- Engineers wire directly to model SDKs or REST APIs.
- No central place to enforce:
- Data type restrictions
- Model choices
- Regions
Failure mode:
- Rogue internal tool sends production PII to a non-compliant region or provider.
- Discovery only happens when a vendor questionnaire or regulatory review forces someone to draw a data flow diagram.
Anti-pattern smell: “We trust engineers to follow the policy.”
Better: Central AI client with policy hooks; code review bots that block direct vendor calls.
3. “Shadow models in production”
Pattern:
- A team tests a new model (or version) by toggling environment variables.
- No formal registration, evaluation, or documentation.
- Output is used for workflows that matter (e.g., KYC triage, credit checks, fraud flags).
Failure mode:
- Vendor silently updates the base model or changes default settings.
- Behavior shifts:
- Regression in edge-cases
- New hallucination patterns
- Different bias profiles
- No paper trail of who approved what.
Anti-pattern smell: “We’ll stabilize this later once we find what works.”
Better: Treat every model + config as a versioned artifact with change control.
4. “Treating eval datasets as non-sensitive”
Pattern:
- Teams collect “real” prompts and responses to improve the system.
- These go into CSVs, labeling tools, or fine-tuning jobs.
- Governance only cares about online traffic, not eval artifacts.
Failure mode:
- Eval sets turn into high-density sensitive corpora: complaints, medical conditions, internal incidents.
- Stored on laptops, shared via email, or uploaded to generic cloud storage with weak controls.
Anti-pattern smell: “It’s just test data.”
Better: Eval and training data should have equal or higher protections than live data.
Practical playbook (what to do in the next 7 days)
You can’t build a perfect AI governance program in a week, but you can de-risk materially.
Day 1–2: Map your actual blast radius
- Inventory where LLMs touch production:
- Services calling AI APIs
- Workers or pipelines doing embeddings, summarization, classification
- Internal tools (copilots, chat assistants) connected to production data
- For each, answer:
- Which data sources are touched?
- Which vendors are involved?
- Where are logs and traces stored?
Deliverable: A one-page “LLM data flow” diagram that security/risk can understand.
Day 2–3: Turn policies into simple rules
Meet with security/compliance and define concrete rules for:
- Prohibited data:
- Example: “No card numbers or government IDs to third-party models.”
- Regional constraints:
- Example: “EU customer data can only hit EU-hosted models.”
- Retention:
- Example: “LLM prompts/traces kept 30–90 days max, then aggregated or deleted.”
- Vendor tiers:
- Example: “Tier 1: only approved for non-sensitive content generation.”
These should be expressed as if/then rules you can implement, not prose like “avoid sending sensitive data.”
Day 3–5: Introduce a thin governance layer in code
Implement a minimal “AI gateway” pattern, even if just a shared internal library:
- Provide:
call_model(use_case, input, metadata)instead ofclient.chat.completions.create
- Inside that function:
- Map
use_case→ allowed models + configs - Inspect
metadata(tenant, region, data_type) → allow/deny/transform - Apply:
- Redaction / masking where required
- Region selection
- Emit:
- Structured audit log
- Minimal trace (no raw secrets)
- Map
Goal: No service talks